During a major event, verification failures are not abstract. They show up as abandoned signups, locked-out customers, and support escalations. The good news is you do not need a full rebuild to reduce that risk. A short readiness review, done with the right questions, can reveal where your OTP flow is fragile and what to fix first. Below are 12 questions you can use to pressure-test your verification flow before the spike hits.
What "Event-Ready OTP" Means
Event-ready OTP is simple to define: users receive codes reliably across your key markets, completion rate stays stable when traffic surges, abuse patterns do not flood your channels, and your team can see problems quickly enough to respond.
According to NIST SP 800-63B digital identity guidelines, authentication systems must implement rate limiting, session binding, and fallback mechanisms to maintain reliability during high-traffic periods.
The 12 Readiness Questions
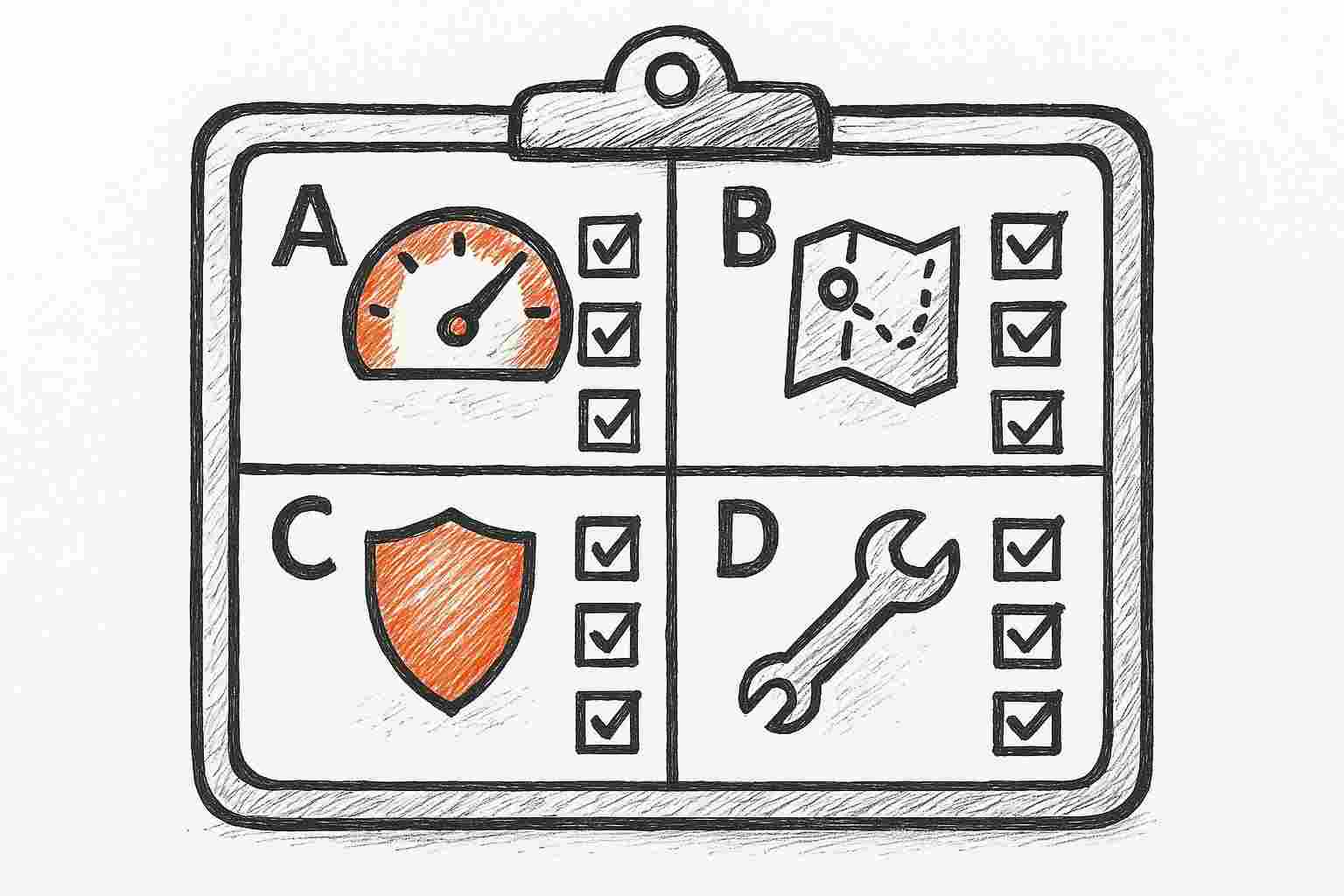
A) Capacity and User Behavior
1) Do you know your peak OTP request volume by flow (login vs registration vs transaction)?
If you only track totals, you will not know where the real risk sits. Registration and checkout flows often spike differently than login flows. Teams that track flow-level volume are 2.3x more likely to identify the correct bottleneck.
2) Do you monitor how volume behaves in bursts, not just daily totals?
Peak events create "worst-minute" behavior. Industry data from Sinch shows peak-minute traffic can be 8-12x higher than the daily average. Monitoring requires per-minute granularity.
3) Do you control resends to prevent resend storms?
Aggressive retry policies during traffic bursts can amplify message volume by 3-5x, increasing filtering risk and queue congestion. Bounded retries with cooldowns are essential.
B) Deliverability and Resilience
4) Can you see success and failure by market and channel?
Carrier filtering behavior varies significantly by route during high-traffic periods, with some carriers becoming 40-60% more aggressive in filtering message patterns.
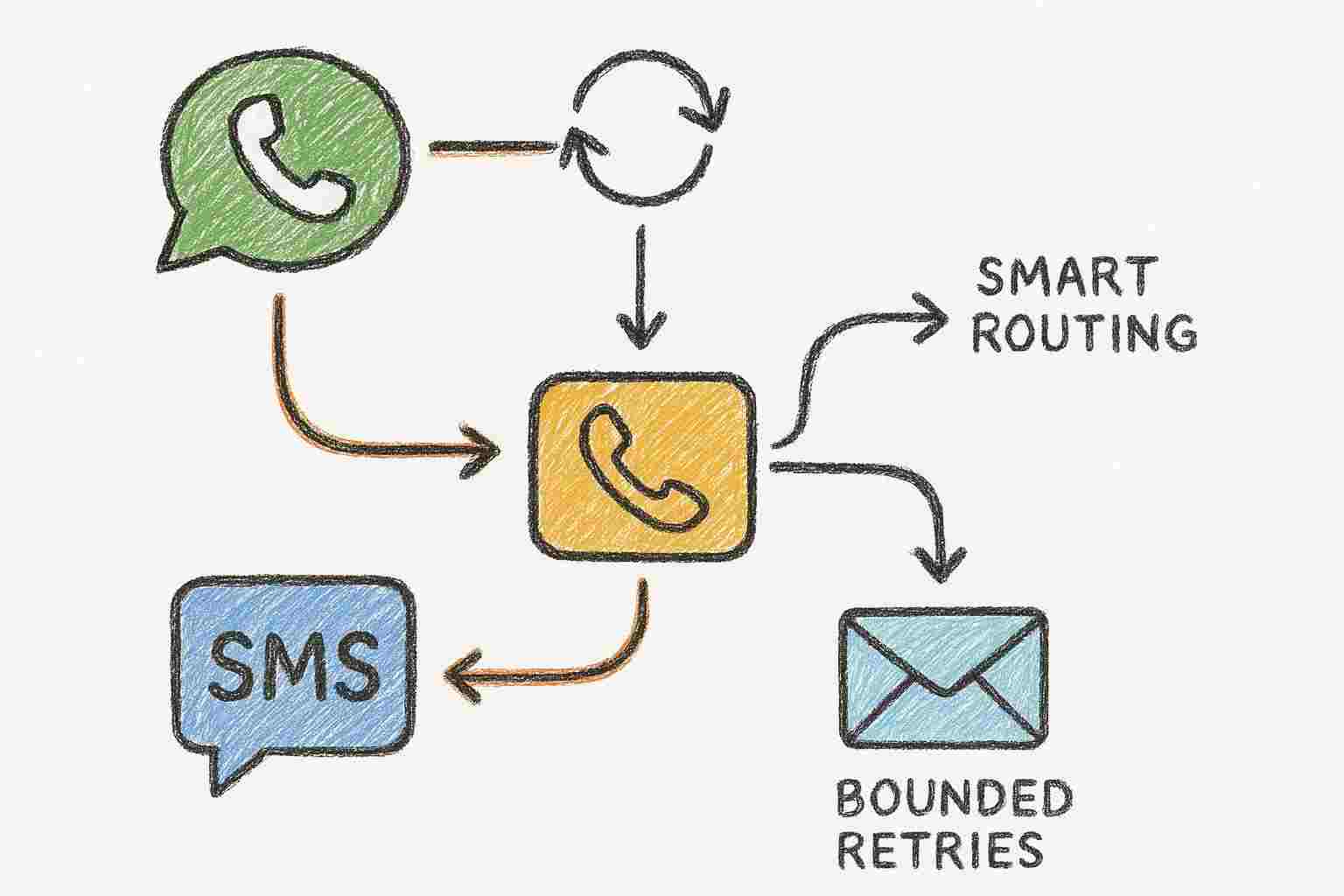
5) Do you have a fallback path for critical flows in your top markets?
Multi-channel verification strategies reduce verification failure rates by 35-50% compared to single-channel SMS. Your critical flows need at least one fallback (WhatsApp, email, or voice).
6) Are retries bounded and designed to reduce congestion?
A safe posture includes: a maximum retry cap (2-3 attempts), exponential backoff, and stopping retries once the user completes verification.
7) Can you prioritize OTP traffic over non-critical messaging?
Transactional verification traffic must have clear priority. High-volume promotional sends can starve your most time-sensitive verification flows if not segmented.
C) Security, Compliance, and Trust
8) Do you have protections against OTP bombing and automated abuse?
Abuse patterns can increase fraudulent load by 200-400% during peak events. Rate limiting per phone number, per IP, and per flow is the minimum baseline.
9) Are Sender IDs and templates ready for the markets that matter?
Template mismatches are a leading cause of delivery failure. Sender IDs must be registered and approved in each target market to comply with local carrier requirements.
10) Can you explain what happened during an incident using delivery reports?
Teams with real-time DLR visibility resolve peak incidents 40% faster. Alert on changes, such as DLR freshness worsening or resend volume spiking.
D) Operations
11) Do you have a runbook for verification degradation?
A runbook documents the steps to take when verification starts degrading: who to notify, which levers to pull (enable fallback, shift traffic), and how to communicate to users.
12) Do you have a phased rollout plan for improvements?
Phased plans let you start now. Identify highest-risk flows and implement quick wins (resend limits, fallback for critical markets) rather than waiting for a complete overhaul.
How to Interpret Your Answers
Think in three maturity bands:
- Baseline-ready: Basic controls; mild spikes are manageable.
- Event-ready: Fallback where it counts; can respond quickly to degradation.
- Resilient: Can adapt during the event window, by market, without chaos.
A Quick Win Plan You Can Start This Week
- Set resend limits to prevent 3-5x message amplification.
- Add a fallback channel to reduce single-channel dependency by 35-50%.
- Define transactional priority so OTP is not starved by promotional sends.
- Document a simple runbook for the first 15 minutes of an incident.
Where EngageLab OTP Can Help
If your answers point to single-channel dependence or limited visibility, EngageLab OTP is built for scale:
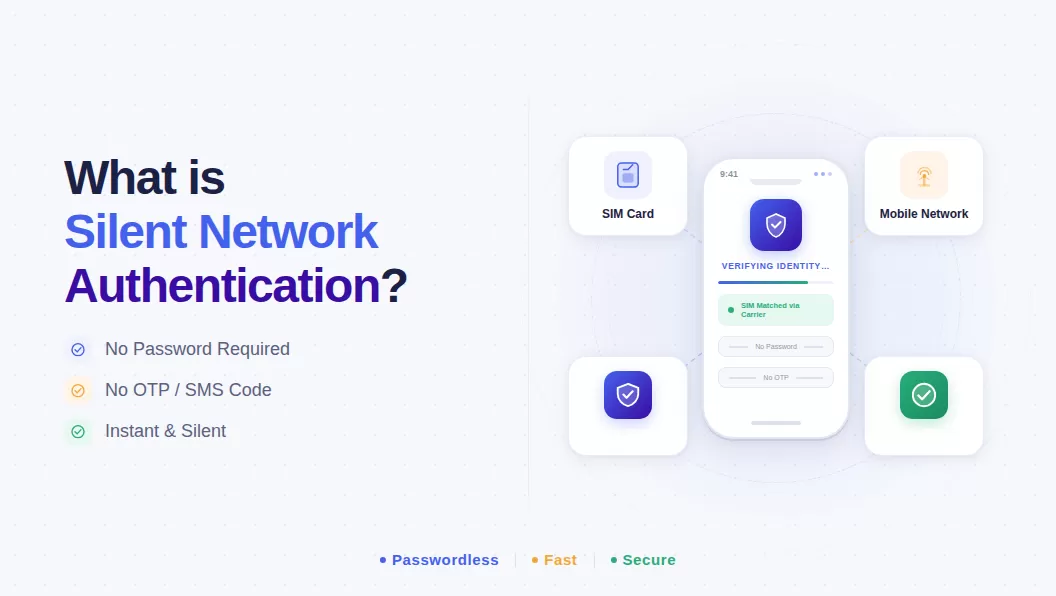
- Multi-channel OTP: SMS, email, WhatsApp, and voice with automatic fallback.
- Smart routing: Automatic retry with bounded caps and route-aware logic.
- Localized templates: Sender identity support across global markets.
- Abuse detection: Rate limiting to protect channel capacity.
Frequently Asked Questions
What does "event-ready OTP" mean?
It means users receive codes reliably across key markets, completion rates stay stable when traffic surges 300-500%, and your team can respond to problems quickly. This requires multi-channel fallback and real-time observability.
What is OTP bombing?
OTP bombing is an abuse pattern where automated systems request verification codes repeatedly for a target phone number. Prevention requires rate limiting per phone number and IP, and anomaly detection tied to your flows.
Why is multi-channel fallback critical?
Single-channel dependence is the fastest path to failure during peak congestion. Multi-channel strategies reduce verification failure rates by 35-50% compared to single-channel SMS during peak events.