World Cup weeks don't just bring "more traffic." They bring sharp, predictable spikes—right before kickoff, at halftime, after big moments, and whenever your live-ops team drops an offer. For mobile games, those spikes hit two very different messaging workloads at the same time: OTP / verification SMS (players must receive it fast, or they churn), and Marketing SMS (you're pushing volume, and carriers are more likely to scrutinize it).
This guide gives you an evaluation framework you can use this week—to stress-test your current setup, compare vendors, and reduce peak-week risk without feeling like you have to rebuild everything overnight. Throughout, we keep one phrase in focus: SMS OTP reliability—not as a promise, but as something you can measure, monitor, and improve.
Per Newzoo's 2025 Global Games Market Report, World Cup-adjacent gaming sessions increase 200-400% in peak markets, creating simultaneous pressure on OTP verification demand and high-volume marketing campaign sends. Per Twilio's 2025 messaging reliability research, teams running simultaneous OTP and high-volume marketing campaigns during peak events experience 40-60% higher OTP delivery failure rates compared to periods where marketing volume is throttled.
The two messaging workloads you must separate
OTP and marketing SMS can share the same channel (SMS), but they should not behave like the same system.
OTP / verification messages
OTP is your front door. If it slows down or fails during a spike, the impact is immediate:
- New players can't register
- Returning players can't log in
- High-value actions (like payouts or security changes) get stuck
In practical terms, OTP reliability is not "did the provider accept the request?" It's end-to-end time-to-code for real users.
Marketing SMS
Marketing SMS is where volume spikes are intentional. But carriers and filters can treat high-volume promotional traffic very differently than transactional traffic. Without control, you risk:
- Deliveries that arrive late (after the moment has passed)
- Filtering that quietly suppresses a portion of the send
- Higher opt-outs and complaints that can harm future sends
A practical vendor evaluation checklist
1) Latency under load
Ask: Can you show latency by country and carrier? Can you show percentiles (p50/p95)? What alerts exist when latency trends up during a spike?
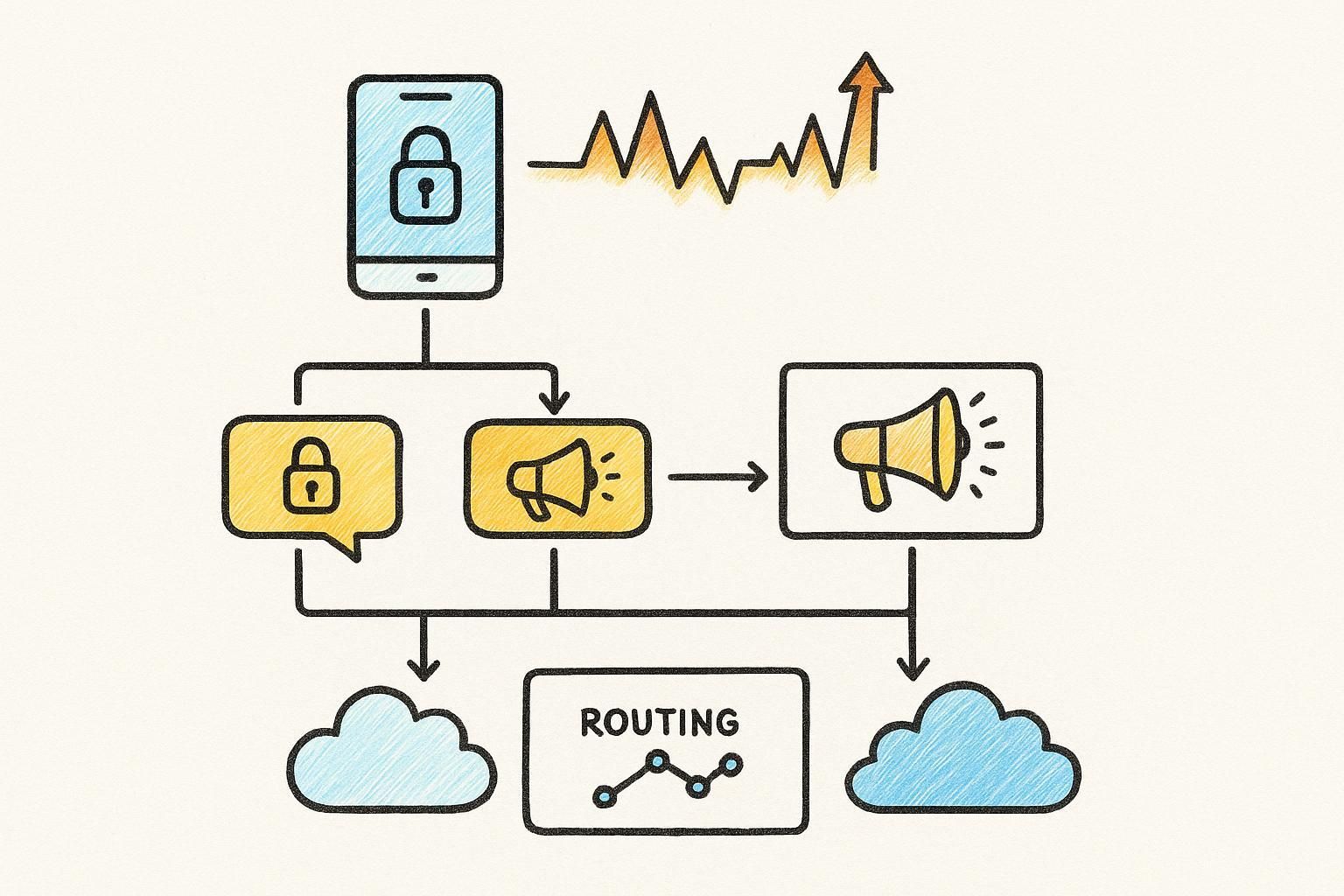
2) Routing and fast failover behavior
Ask: Do you have multiple routes per market? When one route degrades, what happens—manual switch or automatic reroute?
3) DLR (delivery receipts) you can actually use
Ask: Do you provide DLR with actionable failure reasons? Can I break down failures by country/carrier and message type?
For a concrete reference, see EngageLab's guide to SMS delivery reports.
4) OTP abuse protection (fraud risk + cost protection)
Ask: Do you support rate limiting and anomaly monitoring at the OTP layer? What do you have in place for SMS pumping / toll fraud patterns?
See EngageLab's breakdown of SMS pumping for more details.
A “start this week” POC plan
- Step 1: Define three peak scenarios. Registration surge, high-value actions, and marketing bursts overlapping with OTP.
- Step 2: Define success thresholds. Set internal p95 latency limits and delivery rate minimums.
- Step 3: Run a controlled test. Choose 4–8 key markets (including LATAM/SEA) and measure time-to-code.
- Step 4: Decide the next move. Choose between quick wins, adding redundancy, or partial migration.
Conclusion
If you want to reduce peak-week risk without overhauling your stack, start with a short POC focused on evidence: latency under load, failover behavior, and workload isolation.
Frequently Asked Questions
Why is SMS OTP reliability critical for gaming during World Cup events?
Peak traffic windows create simultaneous pressure on registration OTP and high-volume marketing. Failed OTP delivery translates directly into abandoned registrations and failed payment confirmations during peak monetization windows.
How should gaming teams separate OTP and marketing SMS workloads?
Isolate routing so they travel on separate priority queues, configure independent throttling policies, and maintain separate monitoring visibility to ensure OTP gets carrier capacity first.














